-
67
-
116
Magento, starting from 2.3.5, introduced the Content Security Policies (CSP) tool to ensure protection against Cross-Site Scripting (XSS) and related attacks. This is an important means that should not be ignored by shop owners or, what's worse, disabled because it protects customers from card skimmers, session hijacking, clickjacking, etc. Read more about XSS.
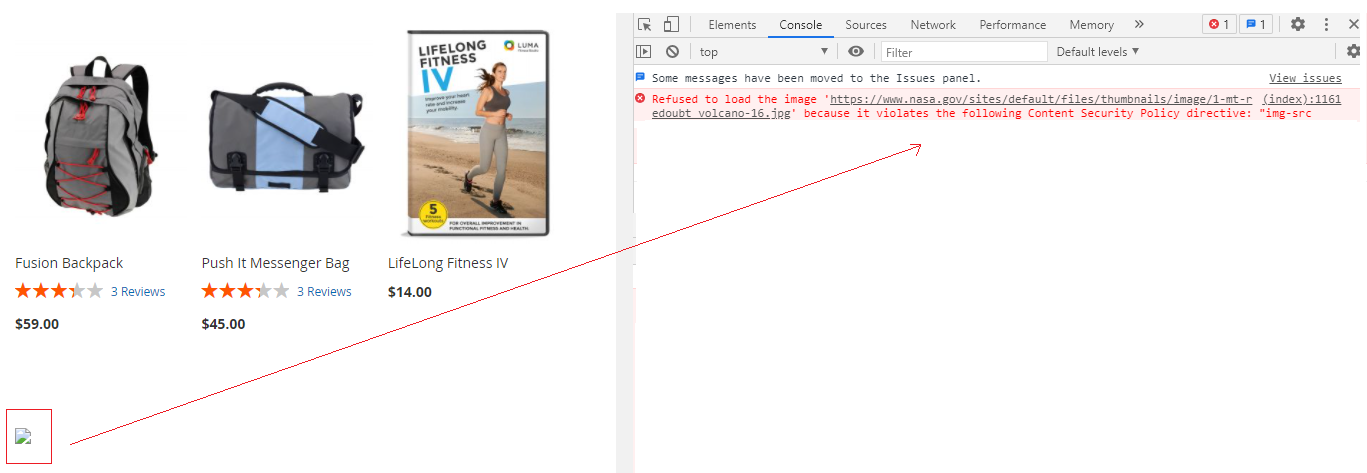
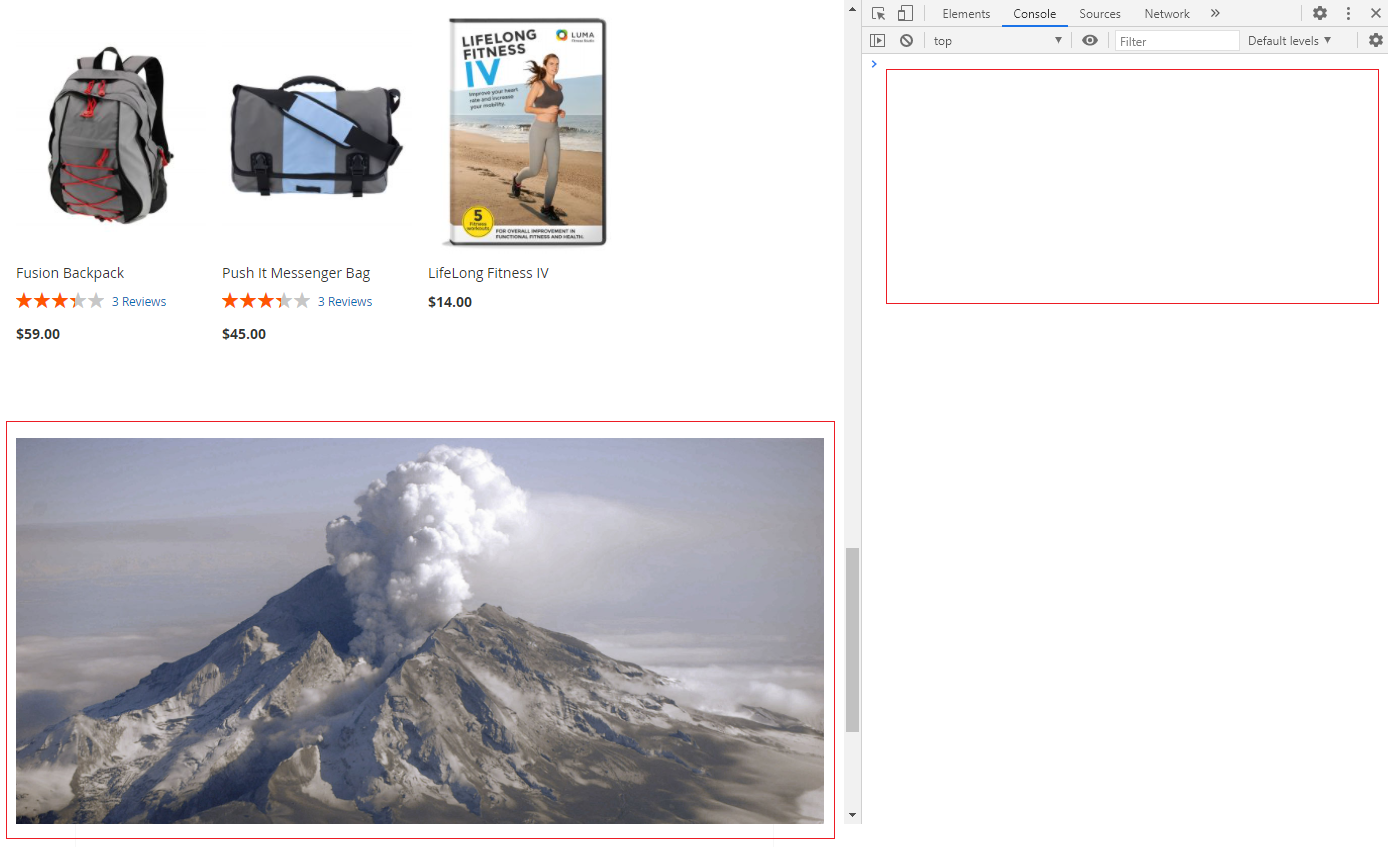
As it usually happens, the new tool brings new headaches to the shop owners. Many external resources used across their websites are not present in the CSP whitelist: YouTube, external images, CDN, Live Chats, various metrics, and services. These either stop working or result in numerous errors in the browser console.
This extension is built to help you organize the CSP whitelist by providing means to view all current policies, add new ones, disable unreliable resources (added by 3rd-party modules), and toggle content security mode from within the Magento admin panel.
Description
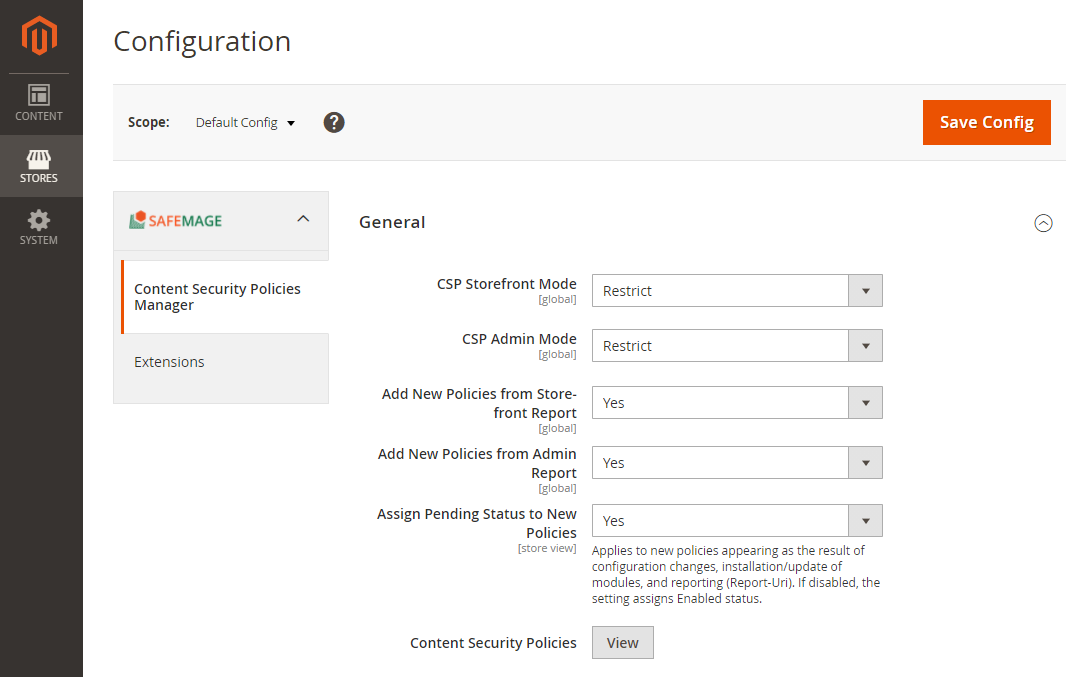
The settings controlling available CSP modes can be found here:
• Stores > Configuration > SAFEMAGE > Content Security Policies Manager
• Restrict – production mode that blocks any hosts not specifically whitelisted.
• Report Only - developer mode, useful for debugging and collecting statistics.
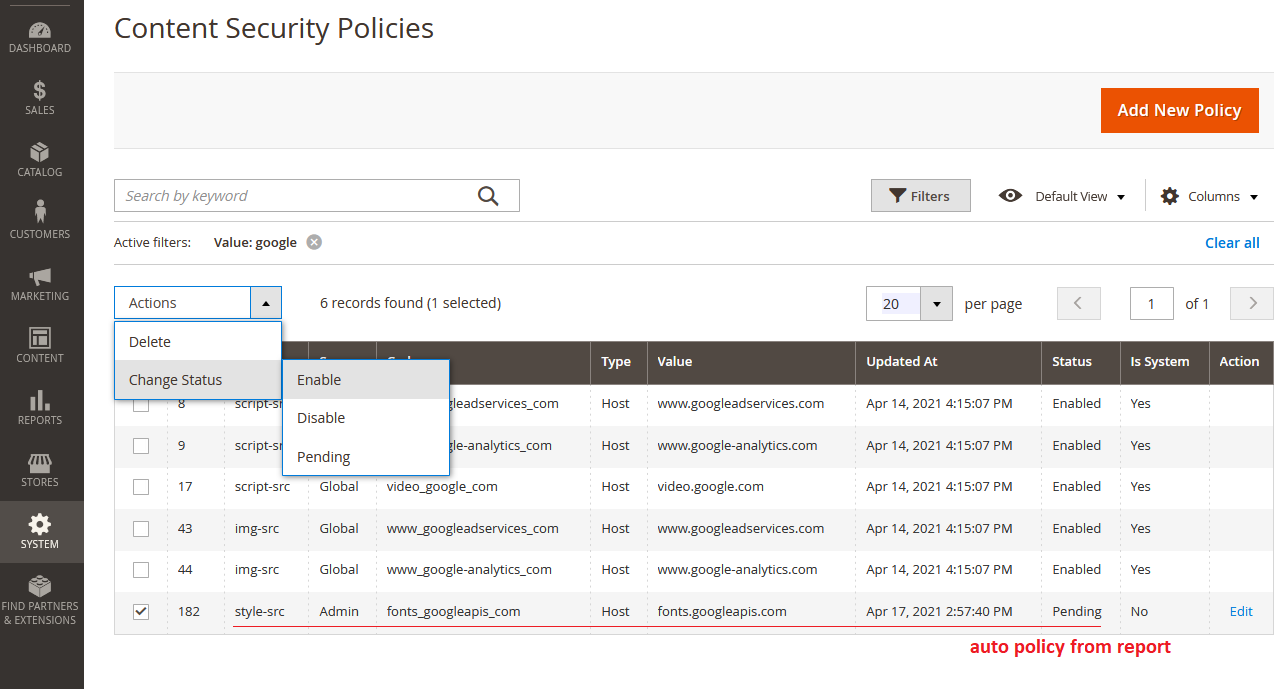
Besides, you can find extra settings that control adding new policies from the report (storefront or admin). The latter collects new CSP from browsers and automatically adds these records to the list. This handy feature would save you time and help you find missing groups and hosts. Should you like to personally approve of new policies and keep new records pending, enable Assign Pending Status to New.
Please note not all browsers support automatic reports. We guarantee proper reporting on recent versions of Chrome, Firefox, Safari. Whenever an untracked CSP host is found on a certain website page, a new record immediately gets added.
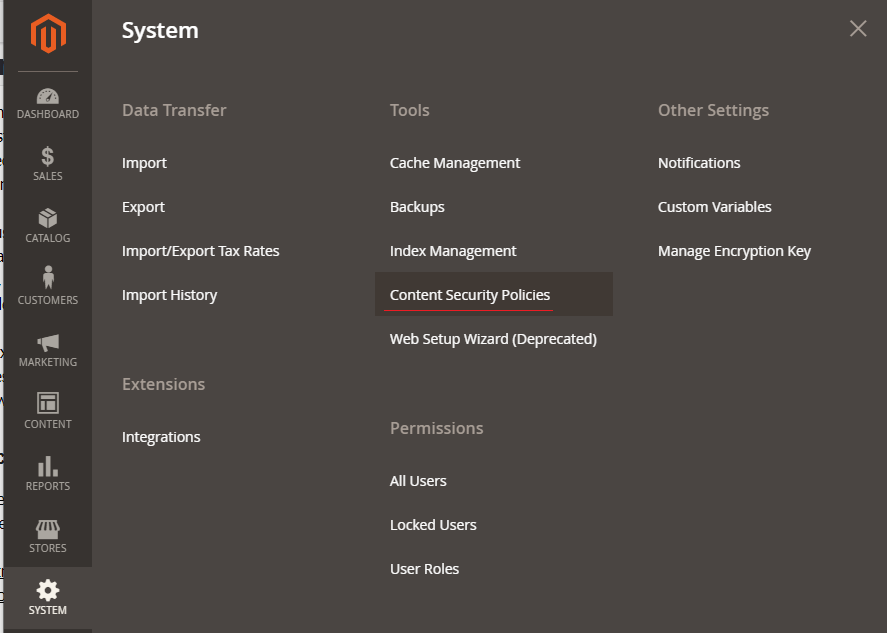
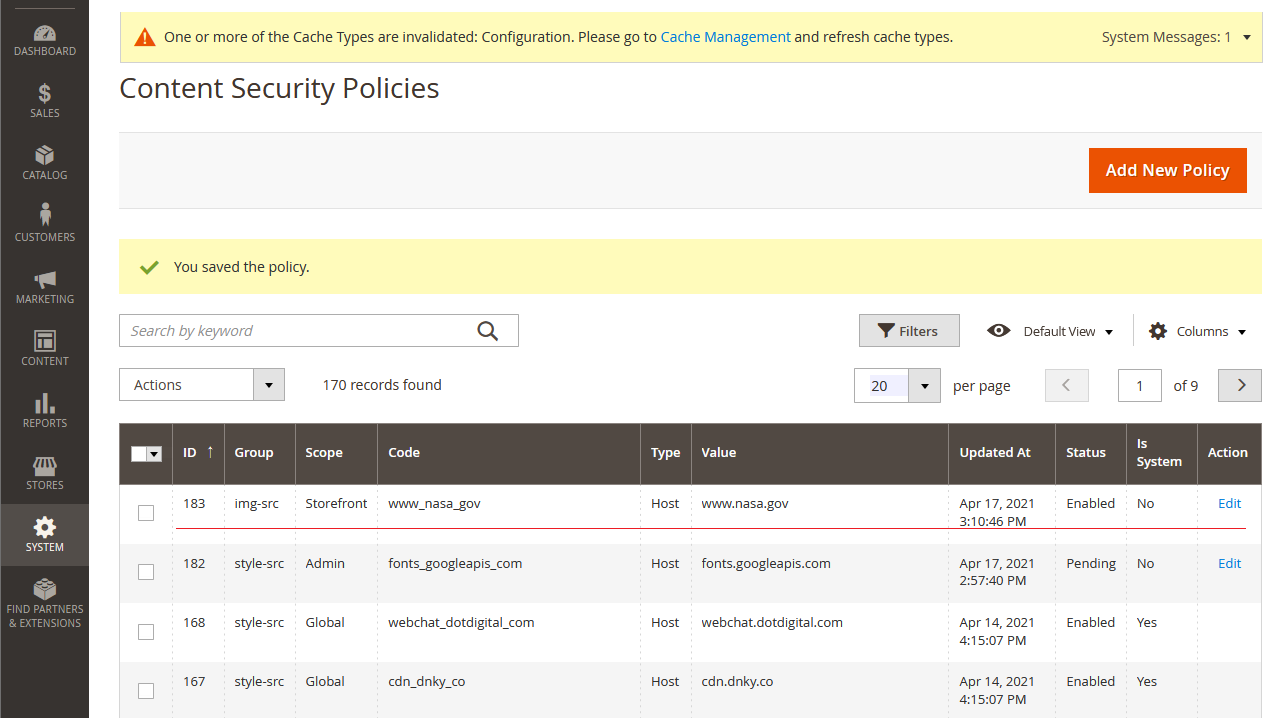
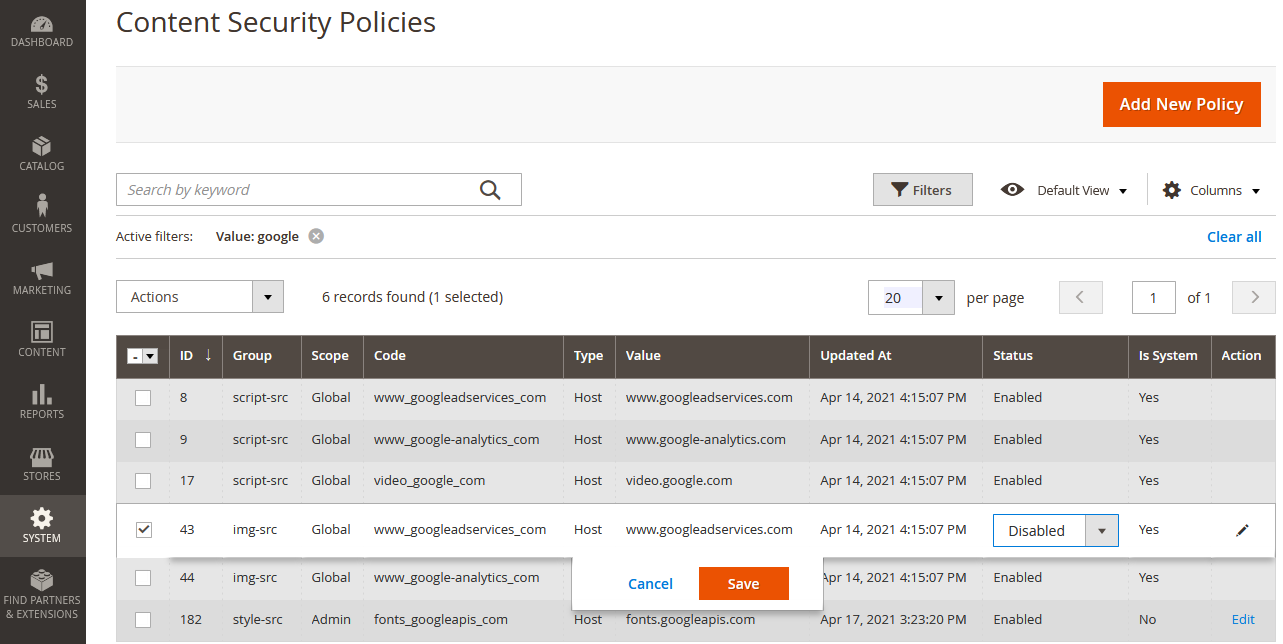
The grid page where all available CSP can be managed is located here:
• System > Tools > Content Security Policies
Statuses can be easily toggled between Disabled and Enabled with the help of mass actions. Note that installing/updating extensions or changing the configuration would result in new pending records appearing in the grid.
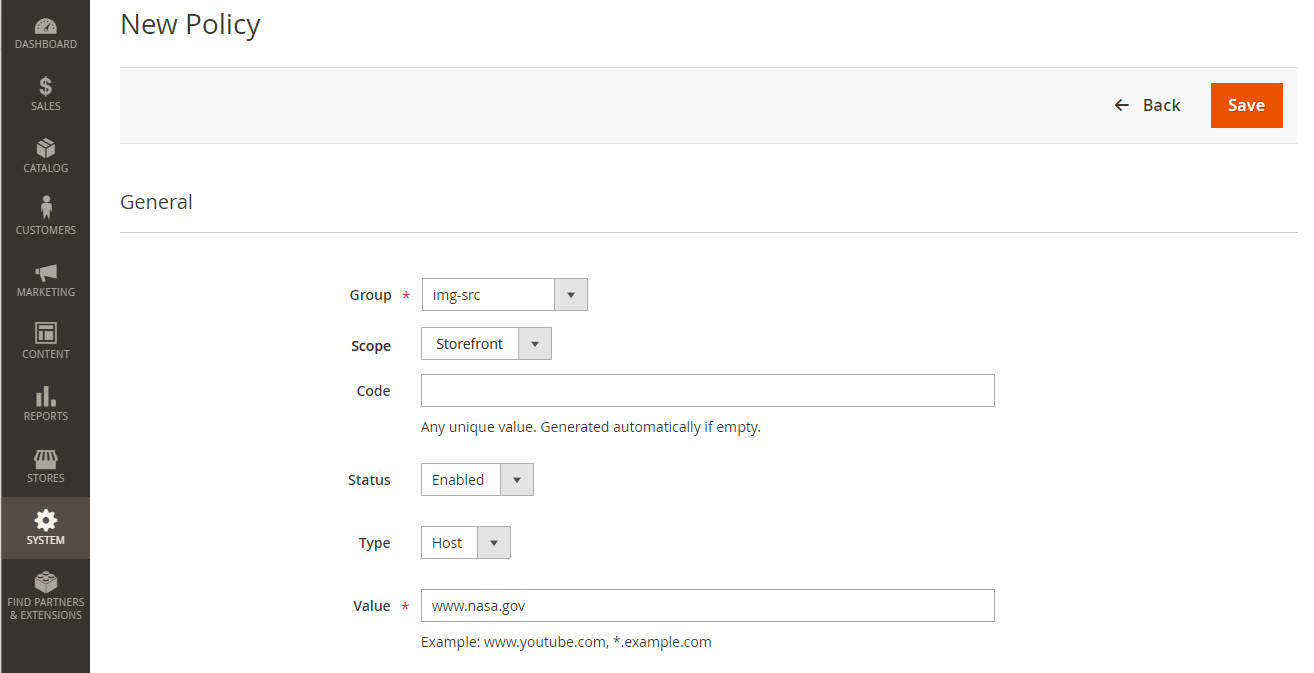
System policies (these can't be deleted, only disabled) are listed by default here. New records can be added, edited, and removed manually. When creating a policy, be careful to select a proper Group. The list below mentions the most common types of CSP.
• font-src – fonts served from external sources
• form-action – valid endpoints for submission from <form> tag
• frame-src – embedded iframes
• img-src – images served from external sources
• script-src – external JavaScript elements
• style-src – stylesheets files
Scope – application area, can be Global, Storefront, and Admin.
Code – any unique value. Generated automatically if empty.
Value – correct source host, e.g., m.youtube.com, *.example.com, etc.
Source – page URL from which a content security data was requested.
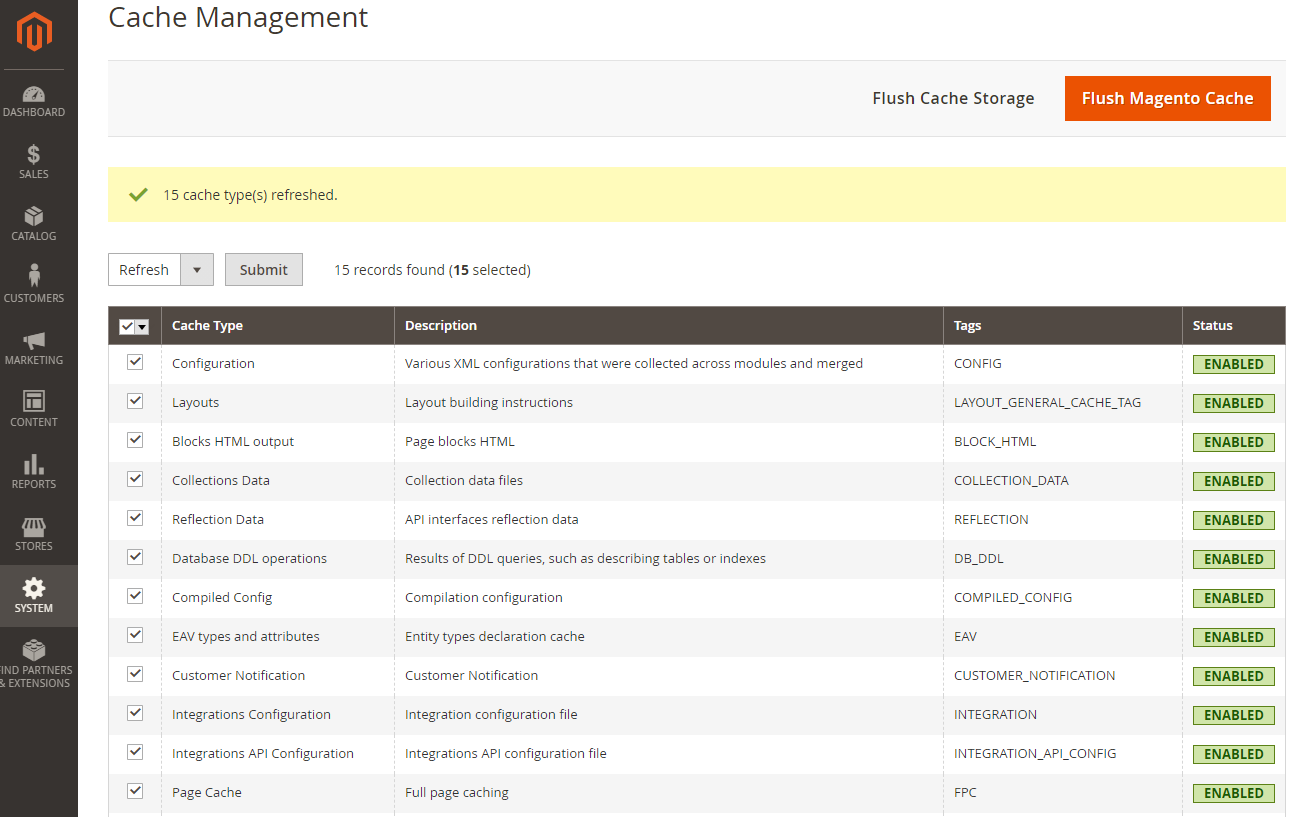
Remember to flush cache whenever you're done making any adjustments.
Features
- Ability to change CSP mode in Magento – restrict or report only
- Displays full policy list in grid view
- Simple means to add new domains with proper group
- Automatically adds new items from browser report to DB
- Disable any unwanted record implemented in 3rd-party module
- Tracks new records on the list after installing or updating extensions
- Deals with `The Content-Security-Policy directive 'frame-ancestors' does not support the source expression ''unsafe-inline''`
Compatibility
Magento Open Source (CE) 2.3.x, 2.4.xMagento Commerce (EE) 2.3.x, 2.4.x
Changelog
new feature bugfix- v.2.4.3 (Jan 25, 2024)
- Addressed a deprecation error.
- v.2.4.2 (Jul 26, 2023)
- Minor code refactoring.
- v.2.4.1 (Dec 13, 2022)
- Added support for “style-src-elem 'self'” and “script-src-elem 'self'” directives for the admin;
- Disabled “unsafe-inline” for 'frame-ancestors' for the admin.
- v.2.4.0 (May 24, 2022)
- Added support for Magento 2.4.4 and PHP 8.1.
- v.2.3.8 (Feb 9, 2022)
- Added support for wildcard (*) when specifying Value.
- v.2.3.7 (Dec 16, 2021)
- Improved error logging added in the previous release.
- v.2.3.6 (Dec 1, 2021)
- Added error logging.
- v.2.3.5 (Nov 29, 2021)
- Added support for “style-src-elem 'self'” and “script-src-elem 'self'” directives.
- v.2.3.4 (Sep 10, 2021)
- Addressed an issue with hash validation when editing policy.
- v.2.3.3 (Sep 9, 2021)
- Improved support for hash-based policies.
- v.2.3.2 (Sep 3, 2021)
- Added support for a new 'script-src-elem' directive.
- v.2.3.1 (Jun 25, 2021)
- Added support for a new 'style-src-elem' directive.
- v.2.3.0 (Aug 20, 2021)
- Now Source renders a full path to the file containing policy (applicable to system policies only in M2.4+);
- The policy table is being locked when new violations are reported and now policies are created;
- Addressed an issue with the Group field sorting.
- v.2.2.7 (Jun 21, 2021)
- Added the ability to disable the Report-To directive.
- v.2.2.6 (Jun 16, 2021)
- Addressed a Magento issue with `directive 'frame-ancestors' does not support the source expression “unsafe-inline'”`.
- v.2.2.5 (Jun 11, 2021)
- Added support for protocol and port in the host field.
- v.2.2.4 (Jun 9, 2021)
- Addressed an issue with duplicate records when a browser reports identical violations simultaneously.
- v.2.2.3 (Jun 8, 2021)
- Addressed an issue with duplicate records sourced from 3rd-party domains.
- v.2.2.2 (May 28, 2021)
- Minor adjustments.
- v.2.2.1 (Apr 21, 2021)
- Addressed an issue with reporting from Safari.
- v.2.2.0 (Apr 20, 2021)
- Added Source and User Agent info.
- v.2.1.1 (Apr 19, 2021)
- Addressed an issue with CSP reports.
- v.2.1.0 (Apr 16, 2021)
- Added the abitlity to add new policies from Report-Uri.
- Added scope: Global, Storefront, Admin.
- v.2.0.0 (Apr 9, 2021)
- Initial release.

Only registered users can write reviews. Please, log in or register